Security is no longer an afterthought in cloud-native environments; it is the absolute foundation. As Kubernetes has become the de facto operating system of the cloud, attackers have shifted their focus to container orchestration layers. Throughout my career building, breaking, and securing infrastructure, I have seen first-hand how a single misconfigured RBAC policy or an exposed dashboard can compromise an entire enterprise cluster. This brings us to the Certified Kubernetes Security Specialist (CKS). If you are a Software Engineer, an SRE, or an Engineering Manager, understanding Kubernetes security is non-negotiable. This guide will walk you through everything you need to know about the CKS certification, how to prepare, and how it fits into your broader career path.
Certification Overview
| Certification | Track | Level | Who It’s For | Prerequisites | Skills Covered | Recommended Order |
|---|---|---|---|---|---|---|
| Certified Kubernetes Administrator (CKA) | Operations / Admin | Intermediate | SysAdmins, Platform Engineers | K8s Basics | Cluster setup, networking, storage, basic troubleshooting | 1st |
| Certified Kubernetes Security Specialist (CKS) | Security / DevSecOps | Advanced | Security Engineers, DevSecOps, SREs | Active CKA Certification | Cluster hardening, supply chain security, runtime monitoring, vulnerability management | 2nd |
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What It Is
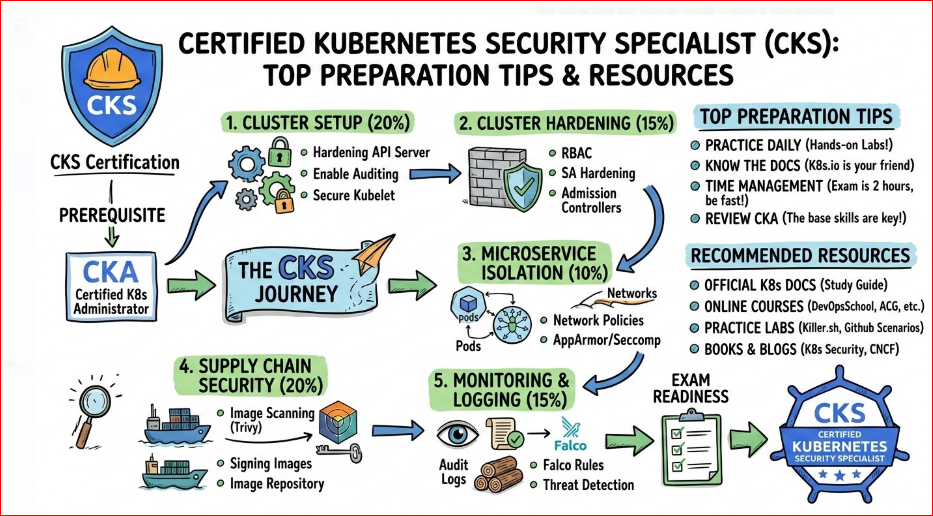
The Certified Kubernetes Security Specialist (CKS) is an advanced, performance-based certification that tests your ability to secure container-based applications and Kubernetes platforms during build, deployment, and runtime. It proves you can defend K8s clusters against both internal and external threats.
Who Should Take It
This certification is heavily recommended for DevSecOps professionals, Security Engineers, SREs, and Platform Engineers who are directly responsible for managing production Kubernetes clusters. Engineering Managers should also understand its concepts to guide their teams in implementing robust security postures.
Skills You’ll Gain
- Cluster Setup Hardening: Restricting access to the API server, configuring RBAC, and implementing network policies.
- Cluster Hardening: Upgrading K8s securely, securing etcd, and managing Kubernetes secrets.
- System Hardening: Minimizing host OS footprint, configuring AppArmor and seccomp profiles.
- Minimize Microservice Vulnerabilities: Managing Pod Security Standards, OPA Gatekeeper, and mTLS.
- Supply Chain Security: Image footprint minimization, image signing, and scanning CI/CD pipelines with tools like Trivy.
- Monitoring, Logging, and Runtime Security: Implementing Falco for runtime threat detection and analyzing audit logs.
Real-World Projects You Should Be Able to Do After It
- Design and deploy an automated image scanning pipeline that blocks vulnerable containers from running in K8s.
- Implement OPA Gatekeeper policies to enforce enterprise compliance (e.g., preventing containers from running as root).
- Deploy and configure Falco to trigger alerts when a shell is spawned inside a production container.
- Lock down an existing Kubernetes cluster by enforcing strict Network Policies, isolating namespaces, and securing the kubelet.
Preparation Plan
Your study timeline depends entirely on your current hands-on experience with Kubernetes.
- 7–14 Days (The Fast Track): For engineers who use K8s daily and recently passed the CKA. Focus entirely on tools like Falco, Trivy, AppArmor, and kube-bench. Take multiple mock exams.
- 30 Days (The Standard Path): For practitioners who passed the CKA a while ago. Spend the first 10 days refreshing K8s primitives, the next 15 days doing hands-on labs with security tools, and the final 5 days on practice exams and time management.
- 60 Days (The Comprehensive Path): For those transitioning into K8s security. Dedicate the first month to deeply understanding Linux security primitives (seccomp, AppArmor, syscalls) and K8s API mechanics. Spend the second month purely on CKS curriculum labs and mock tests.
Common Mistakes
- Failing to manage time: The exam is 100% practical. Spending 20 minutes debugging a single Falco rule will cost you the exam.
- Ignoring Linux primitives: CKS is not just K8s. You must understand Linux systemd, AppArmor profiles, and system calls.
- Over-relying on documentation: While you have access to K8s docs, searching for basic syntax wastes precious time. Memorize your imperative commands.
- Working in the wrong context: Applying a perfect security policy to the wrong cluster or namespace results in zero points.
Best Next Certification After This
After mastering K8s security, the logical next step is architectural leadership. Consider moving toward cloud-native architectural patterns or cloud-specific security certifications (like AWS Security Specialty or Azure Security Engineer).
Choose Your Path
The CKS fits differently into various tech career trajectories. Here are 6 distinct learning paths:
1. DevOps Path
Focus: Continuous integration, delivery, and automation.
Path: Linux Fundamentals → Docker → K8s Basics → CKA → CKS. You use CKS knowledge to secure the pipelines and the deployment manifests you write.
2. DevSecOps Path
Focus: Integrating security natively into the DevOps lifecycle.
Path: K8s Basics → CKA → CKS → Cloud Security Certifications. For you, the CKS is the holy grail. It proves you can shift-left K8s security and protect the runtime.
3. SRE (Site Reliability Engineering) Path
Focus: Reliability, observability, and incident response.
Path: CKA → K8s Troubleshooting → CKS → Observability Certs. CKS helps you understand how security incidents impact reliability and how to securely debug K8s issues without exposing the cluster.
4. AIOps / MLOps Path
Focus: Managing AI/ML workloads at scale.
Path: Docker → K8s Basics → CKA → CKS. ML workloads often require high privileges, GPU access, and vast data access. CKS teaches you how to run these workloads without compromising the underlying cluster.
5. DataOps Path
Focus: Secure, scalable data pipelines.
Path: Database Fundamentals → Cloud Data Certs → CKA → CKS. Data on K8s (like Kafka or Spark) requires strict access control. You will use CKS principles to isolate data namespaces and secure K8s secrets.
6. FinOps Path
Focus: Cloud cost optimization.
Path: Cloud Practitioner → FinOps Certified Practitioner → K8s Basics. While CKS isn’t a primary FinOps cert, understanding K8s security helps FinOps practitioners realize the compute costs of security tools (like DaemonSets for runtime scanning) and optimize them safely.
Role → Recommended Certifications Mapping
| Role | Recommended Certifications | Why It Matters / Context |
|---|---|---|
| DevOps Engineer | CKA + CKS | Ensures your CI/CD pipelines and Kubernetes deployments are fundamentally sound and secure by default. |
| Site Reliability Engineer (SRE) | CKA + CKS | Helps you design highly resilient, attack-proof infrastructure architectures and debug incidents securely. |
| Platform Engineer | CKA + CKS + Service Mesh Certs | You build the internal developer platform; it must have baked-in security, strict RBAC, and automated guardrails. |
| Cloud Engineer | Cloud Architect (AWS/Azure/GCP) + CKA | The CKS is a massive bonus if your enterprise cloud environment heavily relies on managed K8s (EKS, AKS, or GKE). |
| Security Engineer | CompTIA Security+ / CISSP + CKS | Bridges the critical gap between traditional enterprise security policies and modern cloud-native container defense. |
| Data Engineer | Cloud Data Engineer Cert + CKA | The CKS is optional but highly valuable if you manage, isolate, and secure your own K8s data infrastructure (like Spark or Kafka). |
| FinOps Practitioner | FinOps Certified Practitioner | The CKS is generally not required, though understanding K8s resource limits helps optimize the compute costs of security tools. |
| Engineering Manager | CKA (for conceptual understanding) | Taking the CKS exam is usually too deep into the weeds, but understanding the CKS syllabus is critical for guiding your team’s security posture. |
Next Certifications to Take
Once you have the CKS, where do you go from here?
Option 1: Same Track (Deep K8s Expert)
Certified Kubernetes Service Developer (CKAD) or Istio/Envoy Certifications. If you want to stay strictly in the cloud-native/CNCF ecosystem, learning Service Mesh (which handles mTLS and complex network routing) is the natural evolution of K8s security.
Option 2: Cross-Track (Cloud Security Integration)
AWS Certified Security – Specialty or Azure Security Engineer Associate. Kubernetes does not exist in a vacuum. It runs on a cloud provider. Cross-training in the specific security IAM, networking, and KMS features of your underlying cloud makes you a holistic security architect.
Option 3: Leadership (Strategic Security)
CISSP (Certified Information Systems Security Professional) or CISM. If you want to move from engineering into a Staff Engineer, Principal, or CISO role, you need to understand governance, risk, compliance (GRC), and enterprise-wide security management.
Top Institutions for CKS Training & Certification
Finding the right training partner is vital for a complex, hands-on exam like the CKS. Here are top institutions providing training and certification assistance:
DevOpsSchool
DevOpsSchool is a premier destination for mastering K8s security, offering comprehensive bootcamps that perfectly align with the CKS syllabus. Their hands-on labs and expert-led sessions prepare engineers for real-world cluster hardening. They are the official provider for the K8s certification paths mentioned in this guide.
Cotocus
Cotocus specializes in IT consulting and high-level training, bringing deep industry expertise to their K8s security modules. Their training methodology focuses on solving actual enterprise use cases, ensuring students understand both the “how” and the “why” of K8s security.
Scmgalaxy
Scmgalaxy is well-known for its rich community and deep technical tutorials surrounding CI/CD and DevSecOps. Their K8s training programs heavily emphasize integrating security directly into supply chains, a core component of the CKS exam.
BestDevOps
BestDevOps offers robust learning pathways for professionals transitioning from traditional sysadmin roles into cloud-native engineering. Their CKS modules are praised for breaking down complex K8s security primitives into easily digestible, practical labs.
devsecopsschool.com
As the name suggests, this institution focuses entirely on the intersection of development, security, and operations. Their K8s training is strictly security-first, making them an excellent choice for mastering advanced topics like AppArmor, seccomp, and runtime defense.
sreschool.com
SRE School focuses on K8s from a reliability standpoint. Their training highlights how robust K8s security prevents catastrophic cluster failures and data breaches, perfectly mapping CKS skills to Site Reliability Engineering goals.
aiopsschool.com
AIOps School blends modern operations with artificial intelligence. While their core is AI, their K8s modules teach engineers how to securely host, monitor, and scale automated AI workloads without exposing clusters to vulnerabilities.
dataopsschool.com
DataOps School trains professionals in building resilient data pipelines. Their K8s courses provide critical context on how to secure stateful sets, manage K8s secrets safely, and enforce RBAC for data-heavy applications.
finopsschool.com
FinOps School focuses on cloud financial management. Their training provides a unique perspective on K8s, teaching engineers how to balance the compute overhead of security tools (like vulnerability scanners) with strict cloud budget constraints.
Frequently Asked Questions (FAQs)
1. How difficult is the CKS compared to the CKA?
The CKS is significantly more challenging. While CKA tests if you can build and fix a cluster, CKS tests if you can secure it against active threats. The time constraints are tighter, and the scope of external tools (Trivy, Falco, OPA) is much wider.
2. Can I take the CKS without passing the CKA first?
No. You must hold an active (non-expired) Certified Kubernetes Administrator (CKA) certification to even register for the CKS exam.
3. How long does the CKS certification remain valid?
The CKS certification is valid for 24 months from the date you pass the exam. Because K8s security evolves rapidly, you will need to retake the exam to maintain the credential.
4. What K8s version is the exam based on?
The exam environment is regularly updated to match the latest K8s releases (usually within 4-8 weeks of a minor K8s release). Always check the CNCF official curriculum right before your exam to verify the exact version.
5. Do I need to be a Linux expert to pass?
You don’t need to be a kernel developer, but you must be very comfortable with Linux command-line tools, file permissions, systemd, and specific security modules like AppArmor and seccomp.
6. Are third-party tools heavily featured in the exam?
Yes. Unlike the CKA, the CKS specifically requires you to know how to use CNCF ecosystem tools such as Falco (for runtime security), Trivy (for image scanning), and OPA Gatekeeper / Kyverno (for admission control).
7. How much time is given for the exam?
You have exactly 2 hours to complete 15-17 performance-based tasks. Time management is usually the biggest hurdle for candidates.
8. Can I use my own bookmarks during the exam?
No. Recent changes to K8s certification exams restrict candidates to a locked-down browser environment. You will have access to specific K8s documentation URLs within the exam interface, but personal bookmarks are not allowed.
9. Does the CKS have any multiple-choice questions?
No, there are zero multiple-choice questions. It is 100% hands-on command-line tasks in a live Kubernetes environment.
10. How valuable is the CKS for career growth?
Extremely valuable. As companies shift to microservices, the demand for engineers who can securely configure K8s far outpaces the supply. It is a highly respected credential that often leads to senior DevSecOps or Platform Engineering roles.
11. What is the passing score?
You need a score of 67% or higher to pass the CKS exam.
12. If I fail, do I get a free retake?
Yes. Purchasing the exam usually includes one free retake, which must be used within the validity period of your exam purchase (typically 12 months).
Here are 8 highly focused and optimized FAQs for your blog, covering difficulty, time, prerequisites, sequence, value, and career outcomes.
Frequently Asked Questions (FAQs) on CKS
1. Do I need to pass the CKA before taking the CKS?
Yes, holding an active Certified Kubernetes Administrator (CKA) certification is a strict prerequisite. You cannot register for the CKS exam without it, as the security tasks require a deep foundational knowledge of Kubernetes administration.
2. How difficult is the CKS compared to the CKA?
The CKS is widely considered the most challenging Kubernetes certification. While the CKA tests your ability to build and troubleshoot a cluster, the CKS tests your ability to lock it down against active threats under intense time pressure.
3. How much time does it take to prepare for the exam?
This depends on your daily experience. If you use Kubernetes daily and recently passed the CKA, you might only need 2 to 4 weeks of focused study. If you are new to third-party security tools, expect to spend about 60 days practicing in hands-on labs.
4. Is the CKS certification worth the investment for my career?
Absolutely. As enterprises scale their cloud-native infrastructure, container security has become their top priority. The CKS validates a rare, high-demand skill set, making you a prime candidate for senior DevSecOps, SRE, and Platform Engineering roles.
5. Are there any multiple-choice questions on the exam?
No, there are zero multiple-choice questions. The CKS is a 100% performance-based, hands-on exam. You are given a command-line environment and exactly two hours to solve 15 to 17 practical security tasks on live clusters.
6. What external tools do I need to learn for the CKS?
Beyond native Kubernetes features like Network Policies and RBAC, the exam requires you to use specific CNCF and open-source tools. You must be comfortable configuring Falco for runtime security, Trivy for image scanning, and AppArmor for Linux system hardening.
7. How long does the CKS certification remain valid?
Your CKS certification is valid for exactly 24 months from the date you pass. Because cloud-native security tools and threat landscapes evolve so rapidly, the Linux Foundation requires you to recertify to maintain the credential.
8. What happens if I fail the exam on my first attempt?
Do not panic if you do not pass on the first try, as the time limit is strict. Your exam purchase automatically includes one free retake. You can use this retake at any point within your 12-month exam eligibility period.
Testimonials
“Before preparing for the CKS, I thought K8s security just meant writing good RBAC rules. The CKS journey completely changed how I view cluster defense. Implementing tools like Falco and Trivy has made our production environments infinitely more secure.”
— Anjali M., Senior DevSecOps Engineer
“As an Engineering Manager, I don’t write K8s manifests daily anymore. But understanding the CKS curriculum allowed me to ask my Platform team the right questions. We recently overhauled our K8s supply chain security directly based on CKS principles.”
— David R., Director of Cloud Infrastructure
“The time crunch on the CKS is real. But the training at DevOpsSchool gave me the muscle memory I needed. I didn’t have to think about syntax during the exam; my hands just knew what to type to lock down the cluster.”
— Rajesh K., SRE & Cloud Architect
Conclusion
Securing Kubernetes is not a one-time task; it is a continuous, evolving discipline. The Certified Kubernetes Security Specialist (CKS) is more than just a badge on your resume—it is a rigorous forge that shapes you into a highly capable cloud-native defender. By mastering cluster hardening, securing the software supply chain, and implementing real-time threat detection, you ensure that the infrastructure running modern applications remains resilient against sophisticated attacks. If you are serious about a career in DevSecOps, Platform Engineering, or SRE, the CKS is the ultimate milestone to validate your expertise. Take the time to practice, build a homelab, break things, and learn how to secure them. Your career—and your company’s infrastructure—will be better for it.